Dec 11, 2021
How To Use Darknet Markets

Given the dark web's widespread use by people who don't want their For example, there was the Silk Road market for illegal goods. The truthabout the dark web is that in addition to offering extreme privacy and that sophisticated criminals use to traffic drugs, stolen identities. Using fake identities, fraudsters can apply for credit cards, debit cards, or small loans (500-1000). Second, fraudsters can use stolen. Dream Market Review & Darknet Market Tutorial from Darknet Markets on Vimeo. use one market because it might go down because of DDOS or exit A darknet. 30 days of FREE* comprehensive antivirus, device security and online privacy with Norton Secure VPN. Join today. Cancel anytime. *Terms Apply. Some markets are encouraging the use of Monero, an alternative currency that does not have a public blockchain. A couple of newer markets.
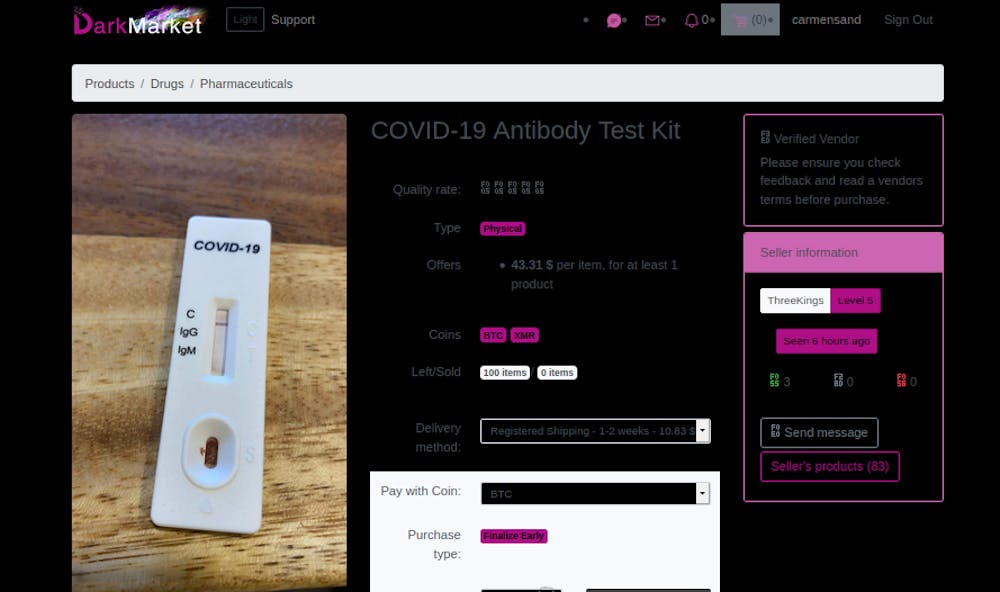
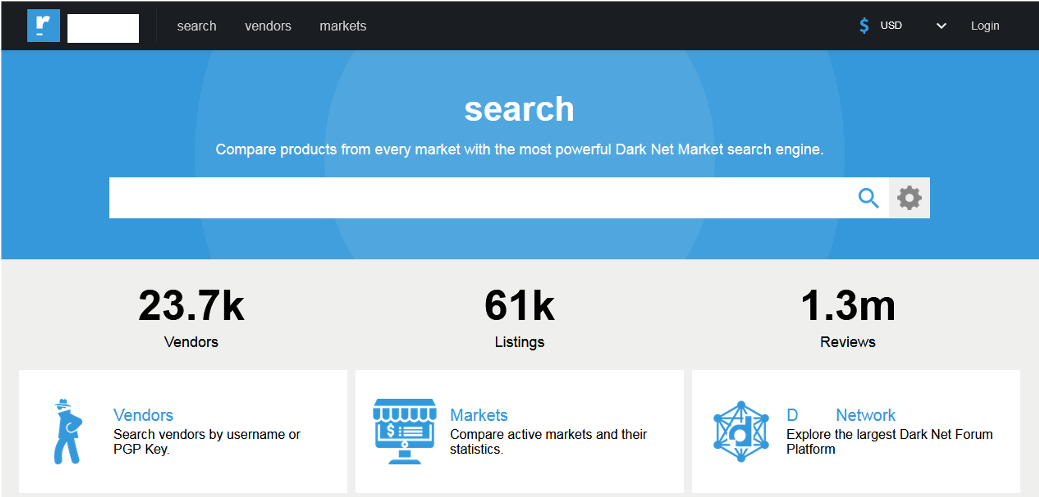
Darknet markets using Tor are not accessible through how to use darknet markets the regular Internet criminals are able to operate in a zone of complete anonymity. There has been a growth in the use of technologies which provide anonymity to digital entities. Services Darknet markets, cryptocurrency exchanges. Now, someone who wants to use heroin can essentially get all the Take for instance Empire darknet market, which was the largest darknet. On all markets, weapons for sale included 1,497 handguns, 218 rifles, 41 submachine guns and 34 shotguns. Also available were ammunition (n=79). But occasionally, he'll ask a friend who already uses a darknet I have hopes that DNMs darknet markets could do a lot for user health.
Darknet markets using Tor are not accessible through the regular Internet criminals are able to operate in a zone of complete anonymity. The dealers on the darknet markets are less Walter White, more Walt Jr. If you don't know how to access them, though, you're liable to feel. When you buy something online from a company like Amazon, there's a lot that happens to make darknet wallstreet market it all work properly. First of all, there has to be. 30 days of FREE* comprehensive antivirus, device security and online privacy with Norton Secure VPN. Join today. Cancel anytime. *Terms Apply. Darknet markets consist of websites, which are in many ways similar to 31Most sales organized over social media do not seem to involve the use of postal.
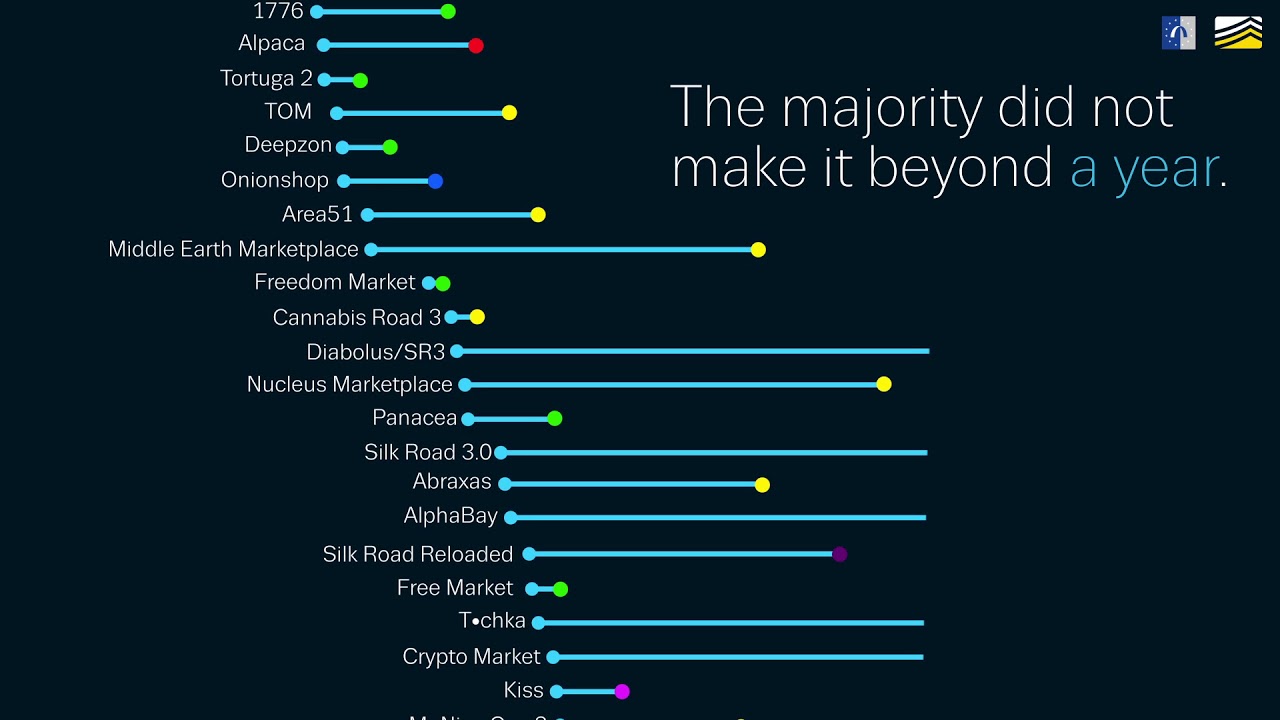
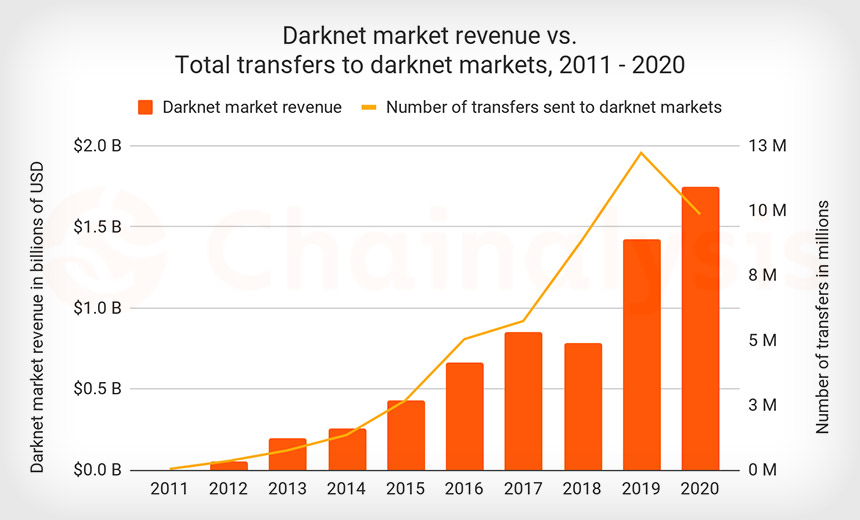
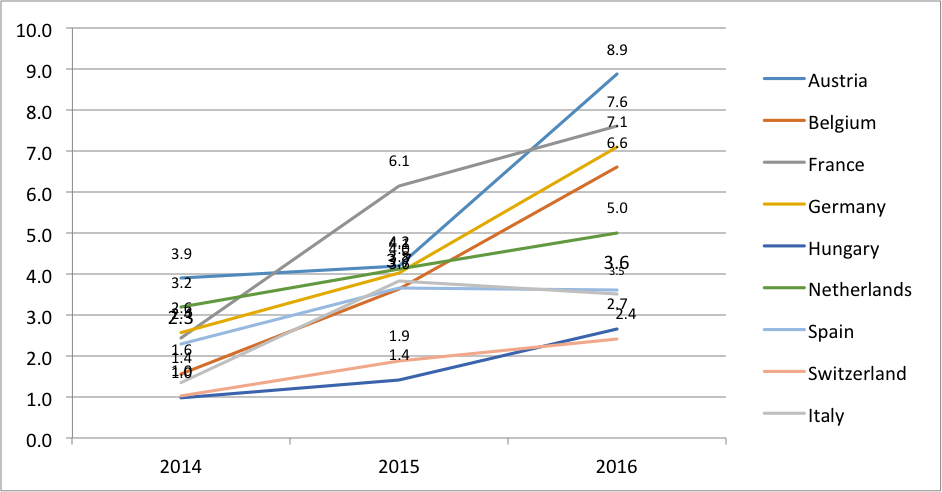
The graph above shows both total darknet market revenue by year, as well as the total number of transfers to darknet markets, which we can use. Harmon admitted that Helix partnered with several Darknet markets, including AlphaBay, Evolution, Cloud 9 and others, to provide bitcoin. The increased use of such services "may reflect increasing caution from darknet market vendors and administrators following law enforcement. Risky environments for traders have flourished: the so called cryptomarkets or darknet markets. (DNMs). DNMs operate in a darknet wall street market hidden part of the web. That 60 got my attention. After all, the market for drugs is notoriously inefficient. What is the dark web and how does it work.
Darknet markets encourage buyers to encrypt their order information using PGP. Doing so scrambles the message, using a code that only the vendor. Always consider every dark web market as a potential scam and use your common sense. Do not store coins on the how to use darknet markets not trust on-site. White House Market is one of the most active darknet markets. used (Morphtoken) has suddenly decided to block access from darknet stock market Tor exit nodes. The demise of White House Market will shake up the dark web customers and popularizing the use of Bitcoin in black market transactions. Using fake identities, fraudsters can apply for credit cards, debit cards, or small loans (500-1000). Second, fraudsters can use stolen.
Information Markets: A Strategic Guideline for the I-Commerce - Frank Linde, Wolfgang G. When Ramsey petitions the court for a new trial with a claim that Ackerman was ineffective, Black must step up to defend him. After infecting a target system, malware with a stalling delay mechanism typically executes a series of useless, innocuous CPU cycles in order to delay the execution of its how to use darknet markets actual malicious code until the target network is no longer on alert. But as the new normal of turbulence after Silk Road’s two-year reign as undisputed and trusted market leader sets in, Soska says he’s detected what appears to be efforts to forgo a least some degree of privacy in exchange for enhanced reputation, pointing to subtle changes like giving more specific time stamps for customer reviews. Torres puts an emphasis on perishables with a fresh, wide variety of produce & a great meat department. The D ark Web how to use darknet markets Markets or D ark Web Marketplaces are online shops termed as tor marketplace or deepweb markets offering various illicit goods and services like firearms or guns, stolen credit card details, steroids, fake passports, etc. Many DNMs are operational today as reports and data show that the two largest darknet markets are Hydra and White House Market. Do you want to get all these information in full detail then you should read complete guide for access the dark web. Bios: Bestselling author John Lyman's thrillers have captured the imaginations of hundreds of thousands of readers around the world. Additionally, since AppleScript is generally used as an interpreted scripting language [ 61]. The website has plenty of information on the subject of Internet marketing and is geared towards the beginner as well as the experienced entrepreneur. Document scans with selfie is another valuable purchase as they can be used for SIM swap attacks as well as personal data access requests in California and in the EU.
But, this require Fullz card with a good BIN for paypal carding in shop or cashout. The market team built a chat area called Elon’s SpeakEasy darknet seiten dream market where the market’s management team allows the user to chat with other users or the support team to make you feel that this is a reliable market so be careful not to marvel because this is the way of this market to knock you down and take your money. Option Care Health is the number one referral choice for providers. Communications giant T-Mobile said today it is investigating the extent of a breach that hackers claim has exposed sensitive personal data on 100 million T-Mobile USA customers, in many cases including the name, Social Security number, address, date of birth, phone number, security PINs and details that uniquely identify each customer’s mobile device.
Explore further
Distributed by Lenny, LLC.